4.7 (588) · $ 1592.00 · In stock
Description
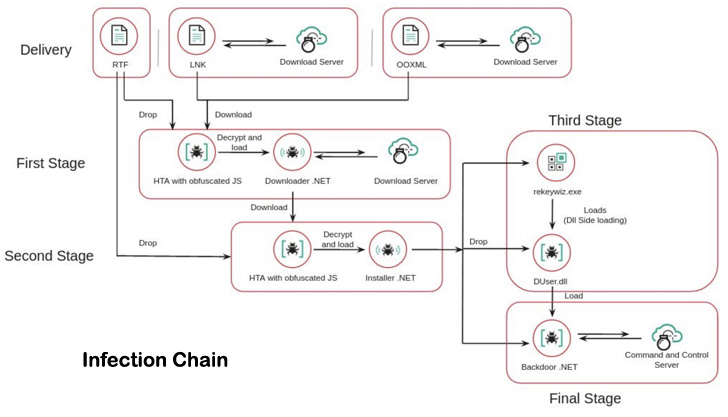
SideWinder Hackers Launched Over a 1,000 Cyber Attacks Over - vulnerability database

Cycldek: Bridging the (air) gap - vulnerability database

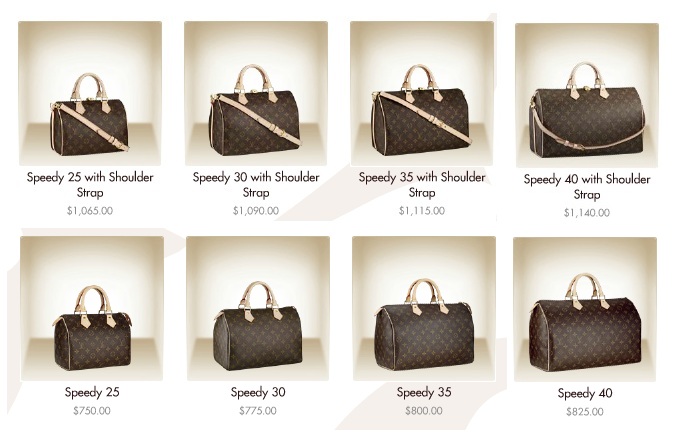
Judging a Person by their Purse – The Hierarchy of Purse Brands: Tier 2. Part 1
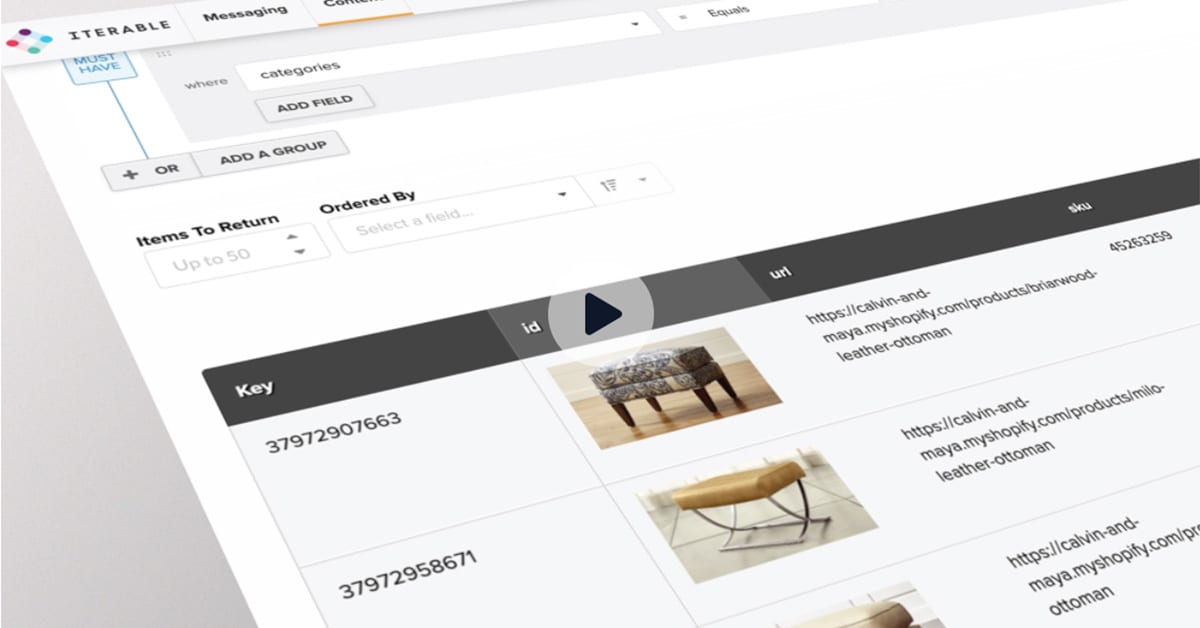
Iterable - Resources about Growth Marketing and User Engagement
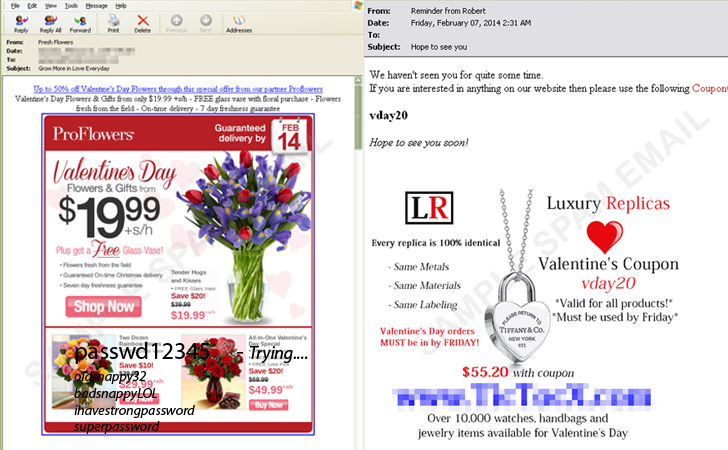
Beware! Cyber Criminals may spoil your Valentine's Day - vulnerability database

The Luxury Brand Hierarchy

SideWinder Hackers Launched Over a 1,000 Cyber Attacks Over - vulnerability database
Privacy_redaction/documents_train.json at master · Priyam05/Privacy_redaction · GitHub

Spam and phishing in Q3 2021 - vulnerability database

From Caribbean shores to your devices: analyzing Cuba ransom - vulnerability database
5etools/data/adventure/adventure-hotdq.json at master · wayne930242/5etools · GitHub
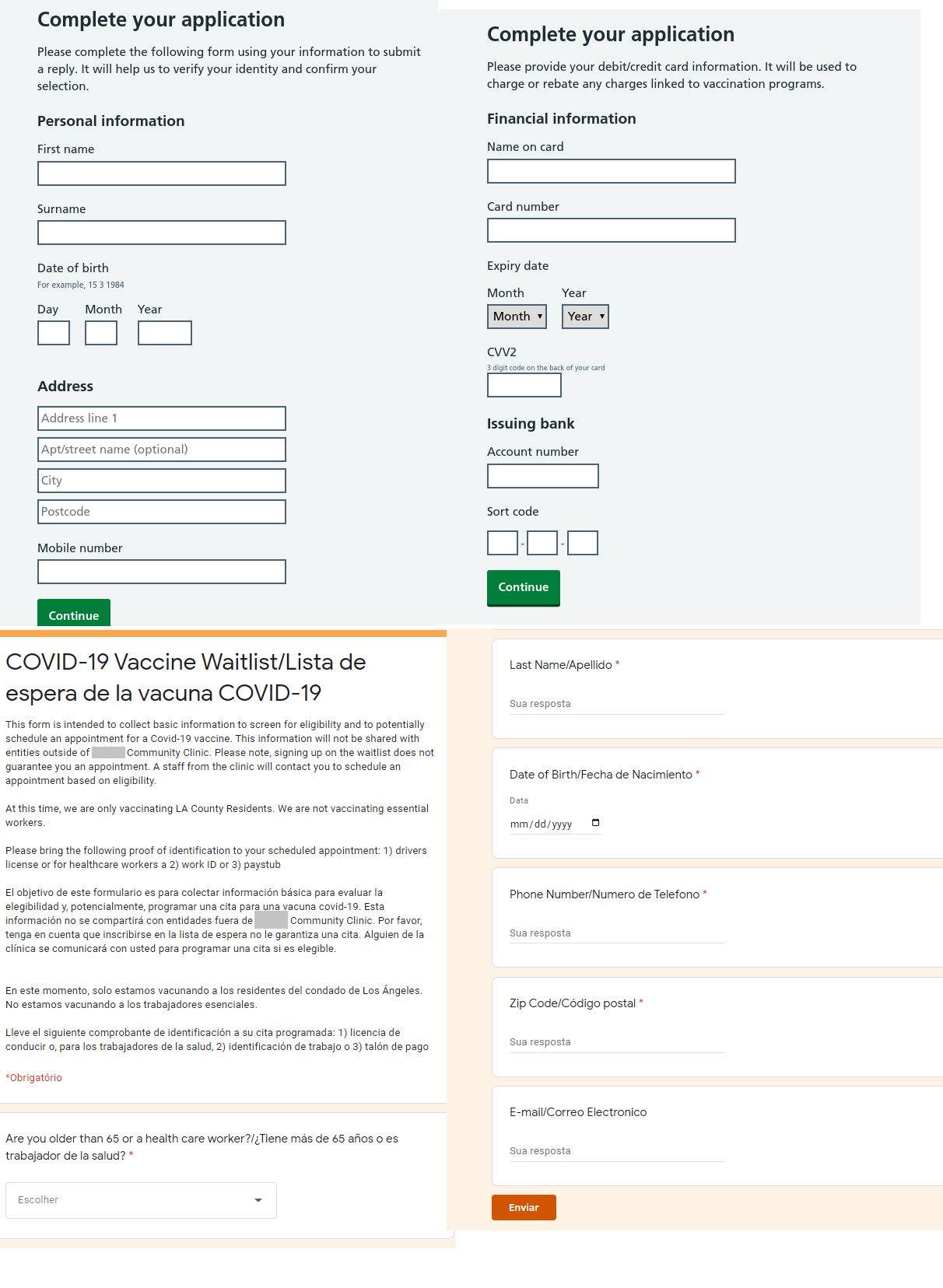
Spam and phishing in Q1 2021 - vulnerability database
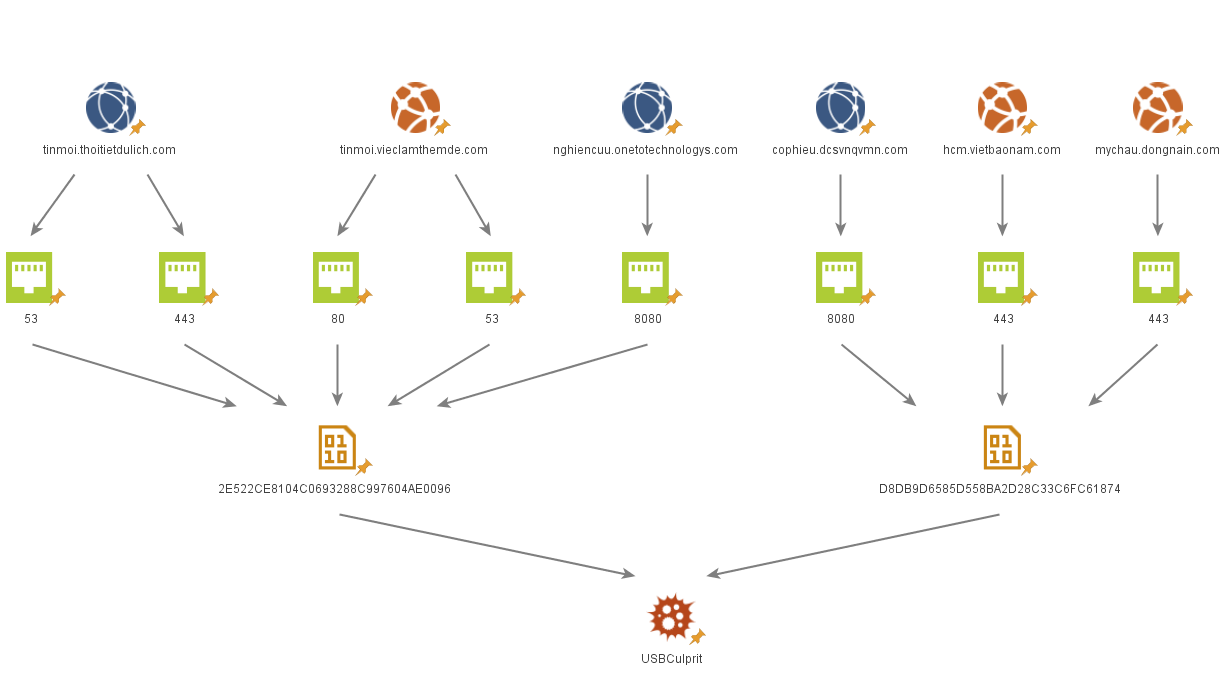
Cycldek: Bridging the (air) gap - vulnerability database